A cursory look at recent headlines reveals two clear trends. First, organizations around the world are embracing digital transformation using technologies across cloud and edge computing to better serve their customers and thrive in fast-paced environments. Second, attackers are constantly innovating new attacks as technology changes and targeting these organizations’ high-value infrastructure with advanced technical capabilities connected to both cybercrime and espionage.
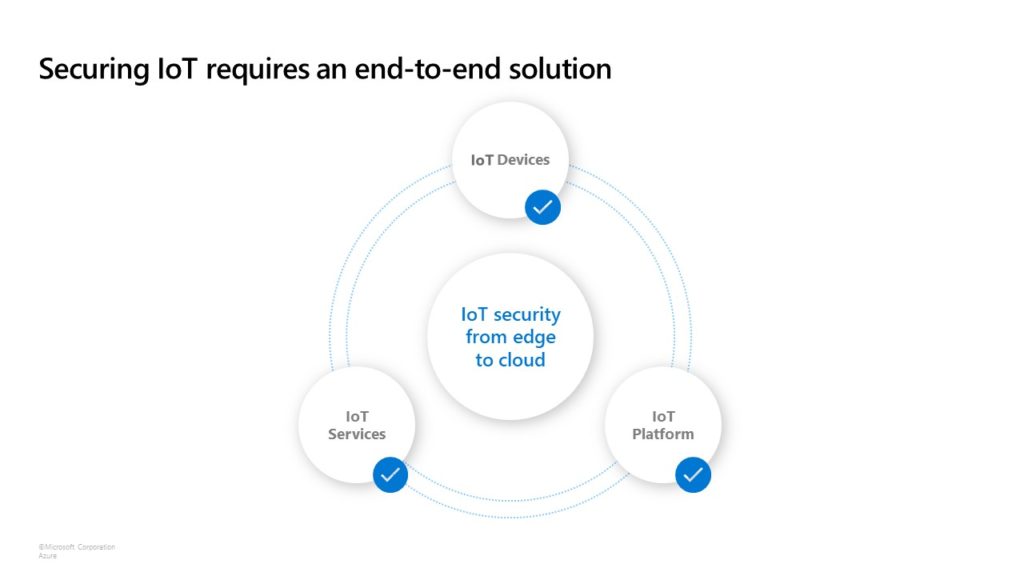
The MagBo marketplace, which sells access to more than 43,000 hacked servers, exemplifies the ever-expanding cybercrime threat. Compromised servers are being exploited to mine cryptocurrency and are being hit with ransomware attacks. Meanwhile, IoT vulnerabilities are on the rise, with more than half of IoT devices deemed susceptible to attack. In addition to these risks, companies often struggle with a lack of expertise and familiarity with security standards as well as complex regulations like the IoT Cybersecurity Improvement Act of 2020.
Given these factors, continuing to raise the security bar for critical infrastructure against attackers and also make it easy for organizations to hit that higher bar is a clear priority for both customers and Microsoft. As systems like the Xbox show, successfully protecting systems requires a holistic approach that builds security from the chip to the cloud across hardware, firmware, and the operating system. Using our learnings from the Secured-core PC initiative, Microsoft is collaborating with partners to expand Secured-core to Windows Server, Azure Stack HCI, and Azure-certified IoT devices, as well as bring the Secured-core values of advanced hardware-based protection and simpler security enablement to the server and IoT ecosystem.
Powerful protection with Secured-core Server and Edge Secured-core
Following Secured-core PC, we are introducing Secured-core Server which is built on three key pillars: simplified security, advanced protection, and preventative defense. Secured-core Servers come with the assurance that manufacturing partners have built hardware and firmware that satisfy the requirements of the operating system (OS) security features. Like Secured-core PC and Secured-core Server, Edge Secured-core advances built-in security for IoT devices running a full OS. Edge Secured-core also expands Secured-core coverage to Linux, in addition to Windows platforms.
Simplified security
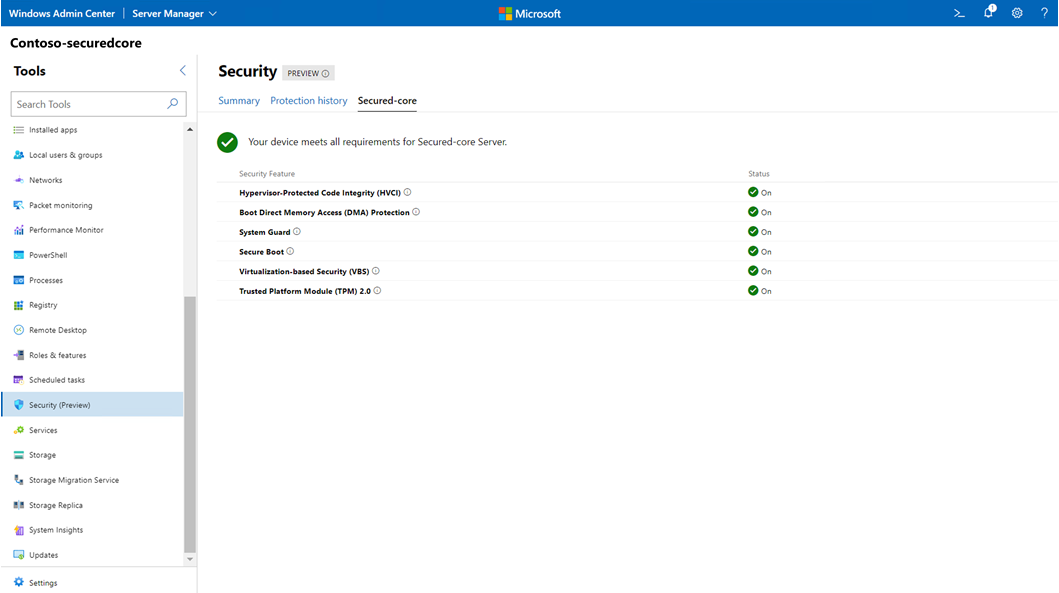
New functionality in the Windows Admin Center makes it easy for customers to configure the OS security features of Secured-core for Windows Server and Azure Stack HCI systems. The new Windows Admin Center security functionality will allow enabling advanced security with a click of the button from a web browser anywhere in the world. With integrated Azure Stack HCI systems, manufacturing partners can also enable OS features, further simplifying the configuration experience for customers so that Microsoft’s best server security is available right out of the box. For Windows Server and validated Azure Stack HCI solutions, customers can look for Secured-core certified systems to simplify acquiring secure hardware platforms.
The Azure Certified Device program already helps customers find the right edge and IoT solutions for their needs. We are adding the Edge Secured-core public preview to the Azure Certified Device program. Edge Secured-core devices meet extra security requirements around device identity, secure boot, OS hardening, device updates, data protection, and vulnerability disclosures, which will be uniquely identifiable on the Azure Certified Device catalog.
Advanced protection
Secured-core Servers maximize hardware, firmware, and OS capabilities to help protect against current and future threats. These safeguards create a platform with added security for critical applications and data used on the server. Secured-core functionality spans the following areas:
- Hardware root-of-trust: Trusted Platform Module 2.0 (TPM 2.0) comes standard with Secured-core Servers, providing a protected store for sensitive keys and data, such as measurements of the components loaded during boot. Being able to verify that firmware that runs during boot is validly signed by the expected author and not tampered with helps improve supply chain security. This hardware root-of-trust elevates the protection provided by capabilities like BitLocker, which uses the TPM 2.0 and facilitates the creation of attestation-based workflows that can be incorporated into zero-trust security strategies.
- Firmware protection: In the last few years, there has been a significant uptick in firmware vulnerabilities, in large part due to the higher level of privileges that firmware runs combined with limited visibility into firmware by traditional anti-virus solutions. Using processor support for Dynamic Root of Trust of Measurement (DRTM) technology, Secured-core systems put firmware in a hardware-based sandbox helping to limit the impact of vulnerabilities in millions of lines of highly privileged firmware code.
- Virtualization-based security (VBS): Secured-core Servers support VBS and hypervisor-based code integrity (HVCI). The cryptocurrency mining attack mentioned earlier leveraged the EternalBlue exploit. VBS and HVCI help protect against this entire class of vulnerabilities by isolating privileged parts of the OS, like the kernel, from the rest of the system. This helps to ensure that servers remain devoted to running critical workloads and helps protect related applications and data from attack and exfiltration.
Edge Secured-core devices come with a built-in security agent, a zero-trust attestation model, and security by default, delivering on the following security features:
- Hardware-based device identity.
- Capable of enforcing system integrity.
- Stays up to date and is remotely manageable.
- Provides protection for data at rest and data in transit.
- Built-in security agent and hardening.
Preventative defense
Secured-core Servers and Edge Secured-core have security mitigations built into the hardware and OS platform to help thwart common attack vectors. Secured-core functionality helps proactively close the door on the many paths that attackers may try to exploit, and it allows IT and SecOps teams to optimize their time across other priorities.
Coming soon, with the support of the ecosystem
Secured-core Servers across Windows Server 2022 and Azure Stack HCI will help customers stay ahead of attackers and help protect their infrastructure across hardware, firmware, and operating systems. Supported hardware will be available in future product generations from Intel, AMD, and our vibrant OEM ecosystem.
“Continuing the rich tradition of innovation in hardware security, AMD is excited to partner with Microsoft to enable Secured-core Server with its future EPYC processors”, said Akash Malhotra, AMD director, security product management. “With attacks on firmware increasing, a tight integration between AMD hardware security features and the Windows Server operating system will benefit users across the ecosystem.”
“Today’s distributed world demands a new era of security. Intel and Microsoft are working together to provide innovative levels of security controls that provide customers with unified, integrated protection,” said Jeremy Rader, General Manager, Intel Cloud and Enterprise Group. “We’re combining the power of Secured core server with our 3rd Gen Intel Xeon Scalable processors (code-named Ice Lake) that creates a chain of trust across all layers of compute, from the hardware, to the firmware to the OS. Customers get a seamless root of trust that combines the most advanced security with management ease.”
You can learn more about Secured-core Servers and Windows Server 2022 security in the related blog.
To get started with Edge Secured-core certification, browse the following resources:
- Learn more about Edge Secured-core.
- Learn more about the launch of the Azure Certified Device program.
- Easily find Edge Secured-core certified devices on the Azure Certified Device Catalog using pre-built certification filters.
- Visit the Azure Certified Device submission portal (requires Microsoft Partner Network membership).
To learn more about Secured-core Servers and Edge Secured-core, be sure to join us during Microsoft Ignite from March 2-4, 2021.








